Identity Theft & How to Protect Against Cyber Attacks (15 Ways)
Cybersecurity may not often be included as part of wealth management, but poor practices could lead to significant financial loss. However, many cases of identity theft can be prevented with prudent practices and security measures.
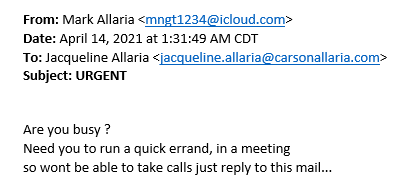
According to Broadbandsearch.net, cybercrime costs the global economy more the $10 trillion per year. Also, roughly 30% of all US consumers were affected by data breaches in 2020. Cybercrime schemes seem to be on the rise as well. Ironically, as I wrote this blog post, I received a fraudulent email from a known contact of mine, whose email had been hacked.
How to Protect Against Cyber Attacks
I don’t claim to be a cybersecurity expert, but I’ve learned enough to know that it’s important to be vigilant in order to protect your personal and financial information. Here are 15 things you can do to protect yourself against cyber-attacks.
1. Credit freeze
A credit freeze, or security freeze, restricts access to your credit report, which makes it more difficult for identity thieves to open new accounts in your name. It’s vitally important to note that a credit freeze is much different, and superior (in my opinion), than a credit monitoring or credit “lock” program. Credit freezes will prevent thieves from opening new accounts in your name. Credit monitoring programs will simply alert you once they’ve done so.
The downside of a credit freeze is that it can be inconvenient if you are trying to secure a new line of credit (credit card, mortgage, new car, etc.). In that sense, a credit freeze works almost too well, as it does not allow you to access your own credit during a freeze. The fix, however, is straightforward. You can apply a temporary lift on your credit freeze if you are expecting to need access to your credit.
An additional downside is that a credit freeze is most effective after implementing with all three credit agencies (Equifax, Experian, and Transunion). Therefore, if you need a temporary lift on your credit, you’ll have to request one at each credit agency.
Although these are minor inconveniences, a credit freeze is a great way to maintain peace of mind that you don’t have fraudulent credit cards or other accounts that have been opened in your name. Here are some FAQs on credit freezes.
Want to create a credit freeze on your credit profiles to help prevent identity theft? Click the links below to access the 3 main credit agencies.
2. Bank account and credit card alerts
Credit freezes are effective at reducing fraud and identity theft on new accounts, but what about existing accounts? Unfortunately, a credit freeze won’t protect you from your current bank and credit card accounts being compromised. That’s why it’s important to set up alerts on both so that you’re aware of suspicious activity. Most credit cards allow you to customize your alerts that fit your spending patterns. The most conservative strategy; set an alert for every transaction.
3. Using credit cards instead of debit cards
This one is straightforward. Credit cards offer far greater fraud protection vs. debit cards. According to Investopedia.com, as long as the customer reports the loss or theft in a timely manner, the maximum liability for purchases made after the card disappeared is $50. For debit cards, the customer can receive the same level of protection, but only if they report the loss or theft within 48 hours. After 48 hours, the customer’s liability rises to $500. After 60 days, there is no limit.
4. Don’t click suspicious links in your email
Have you ever heard the phrase “Curiosity killed the cat?” There is not likely a more relevant saying when discussing suspicious links and phishing attempts. A phishing attempt is when an identity thief tries to trick you into giving your information to them, and they account for 80% of reported security incidents and lead to estimated losses of $17,700 every minute!
These emails may include a message that refers to a “secure message” that needs your attention. The email then might instruct you to click a link to view the message. But, if you are unsure about a link, or perhaps you weren’t expecting anything from the sender, verify with the sender that they did, in fact, send you something before you click. Always pause before you click to examine if you feel it may be a security risk. This can help prevent you from becoming a victim of identity theft.
5. Confirm email senders prior to responding
As referenced above, email is one of the most vulnerable areas of cybersecurity. In addition to not clicking suspicious links, it’s also vitally important to verify the identity of the sender prior to interacting with an email. In many cases, email phishing attempts will appear 100% legitimate, as though they are coming from a co-worker, familiar company, customer, etc., including logos and display names that appear correct (see the snapshot below).
This is an example of how identity thieves will use a correct display name to obtain information. They may also use logos if they are impersonating a company they think you interact with regularly (Amazon, Apple, etc.).
Before interacting, evaluate if the email seems suspicious. Are there typos? Is the language odd? What time was the email sent? In the email above, you can see the email was sent at approximately 1:30 AM, which should immediately raise a red flag as to the legitimacy of the email.
It bears mentioning again, but do not click suspicious links and verify the sender before you interact with a suspicious email. More importantly, when you verify the identity of the sender, contact them using their confirmed email or phone number, and don’t simply hit reply to the email you received.
6. Don’t email attachments with sensitive information
Fielding emails cautiously is important, but the same level of scrutiny is needed when sending emails. The biggest takeaway here is to avoid sending attachments that include personal identifiable information (address, date of birth, account numbers, etc.).
This is especially relevant when you’re working with your accountant, financial advisor, mortgage broker, etc. Even if one of these professionals requests a financial statement, tax return, or something similar, do not send these types of items via email. Instead, request a secure method to share your documents, like a secure online portal. Or, do it the old-fashioned way and drop off a copy in person.
7. Create secret email address for financial accounts with highest level of security
Staying on the email train, consider creating a secret email for your financial accounts, keeping it separate from the email you use for non-financial items. This way, less people will have the email address for financial matters, and you can add the highest level of security to this email address.
8. Use a strong password
One way to increase the security of your email and financial accounts is to use strong passwords. It’s important to avoid passwords that would be easy to guess, like password1234 (if that’s your password, go change it right now!). There are a few methods that can help you create much secure passwords that are easy to remember.
One method is the passphrase method. By combining 3-4 uncommon words, you can increase the security of your password. For example, by using the guide components animal, food, green, patriotic, I might come up with:
TigerPieTreeFlag
These are four unrelated words but fairly easy to remember. To add even more security, you could encrypt using special characters in place of letters, like so:
T!g3rP!3Tr33Fl@g
Another method is the sentence method, discussed more in this article. By using the sentence “I like to hike with my wife on vacation,” you could use the first two letters from each word to make the password:
Ilitohiwimywionva (pretty secure looking!)
9. Consider a password manager
It’s understandably difficult to remember all of your passwords, especially when adding extra levels of encryption and coding. That is where a password manager can assist. A password manager is a computer program that allows users to store, generate, and manage their passwords.
There are several reputable password managers on the market that you could consider, but the main idea is that if you’re going to store your passwords, make sure you do so in a secure location (i.e. not in a Microsoft word file stored on your desktop)
10. Two-factor authentication
Two-factor, or multi-factor authentication adds yet another layer of security to your digital life by requiring two correct pieces of information to access whatever platform you’re trying to access. In practice, two-factor authentication generally involves you entering your correct username and password first, then entering a separate (changing code) that is either emailed or texted to you.
In other words, it’s not enough if a cyber thief gets their hands on your password. They would need to steal your login information and compromise your cell phone or email as well. Two-factor authentication can be added to all kinds of things, including email, software programs, apps, and many other associated logins. You can think of two-factor authentication as a lock behind your lock.
11. Don’t use public/unsecure wifi
Two-factor authentication is great, but if you have two-factor authentication to log in to a secure program on your computer, but then use an unsecured wifi network to access the internet, your efforts could all be for naught. Unsecured wifi networks are common in restaurants, hotel lobbies, or other public places. You’ll know it’s unsecured if the network does not require a password to logon. Here are some tips from the Federal Trade Commission on using unsecured wifi networks.
12. Review your children’s credit
The Federal Trade Commission recommends that you monitor your child’s credit and check for a credit report. Identity thieves can target a child’s identity with the thought that their credit report will not be monitored, making them an unknown victim of identity theft.
For warning signs and how to check your child’s credit, see these tips from the FTC.
13. Never give your financial information to those that call you until their identity is verified
While email and other digital activity is a large source of identity theft, phone scams are another method to be aware of, and identity thieves are becoming more and more sophisticated in their phone tactics. For example, they can make a call appear like it is coming from a phone number that it is not. When you answer, they will likely know your name and may even be aware of a financial institution you work with.
The key here is to never provide your personal financial information over the phone from an incoming call. Gather information regarding their request, then hang up and call them back using a publicly listed phone number. If you willingly give your information, or worse, authorize a wire transfer over the phone, you are not likely to ever recoup your losses.
14. Beware of phishing text messages (if you’re not expecting it, delete it)
While phone and email schemes have been around for a while, text scams are relatively new, but on the rise. However, the same principles apply. If you don’t recognize the number, or if you aren’t expecting a text, don’t interact with the text. Do not reply and definitely do not click any links. If you’re unsure, contact the alleged sender using a different contact method or publicly-listed phone number.
15. Don’t post vaccine selfies with vaccine cards
In the age of COVID vaccines, we’re seeing more and more vaccine selfies being posted on social media (pictures of yourself with your vaccine card). Although this is done with a positive intent, these vaccine cards contain pieces of sensitive information, like your date of birth and patient number, and could cause vulnerabilities with the security of your identity/medical records.
So, if you want to post a vaccine selfie, make sure to cover up the sensitive information on your vaccine card!
Bottom Line
There are so many things to think about when discussing identity theft that it can sometimes feel overwhelming. However, the key is to remain vigilant in your actions across all platforms. For more learning, we recommend grabbing a copy of “The Secret to Cybersecurity,” a book written by former FBI agent Scott Augenbaum. If you’re worried that you may be a victim of identity theft, you can go to www.haveibeenpwned.com and see if your information has been compromised.
Whatever you do, we encourage you to embrace these practices, as the world of cybercrime is not likely to go away. The good news is that many of the losses that result from cybercrime are preventable, as long as you can carry out these simple principles. Doing so will keep more money in your pocket, and more peace in your mind.

Joe Allaria, CFP®
Wealth Advisor | Partner
Free Retirement Assessment
Our free assessment will show you how to invest confidently, reduce taxes, and retire successfully.
We want you to know exactly how we can help before you pay us a single dollar.